Crime has moved to the cloud.
Our response is still stuck on the pavement.
The boundary between our physical streets and digital networks has effectively vanished. Today, a threat to a local community is just as likely to originate in a decentralised server half a world away as it is on a street corner. While organised crime and hostile actors move with the speed of a global startup, our institutions are still grappling with the "institutional lag" of legacy systems and bordered thinking.
In Designing the Future Ready Force, I set out a roadmap for a converged world. We can no longer afford to treat "cyber" as a separate department. It is the environment in which all modern conflict now lives.
What we cover in this brief:
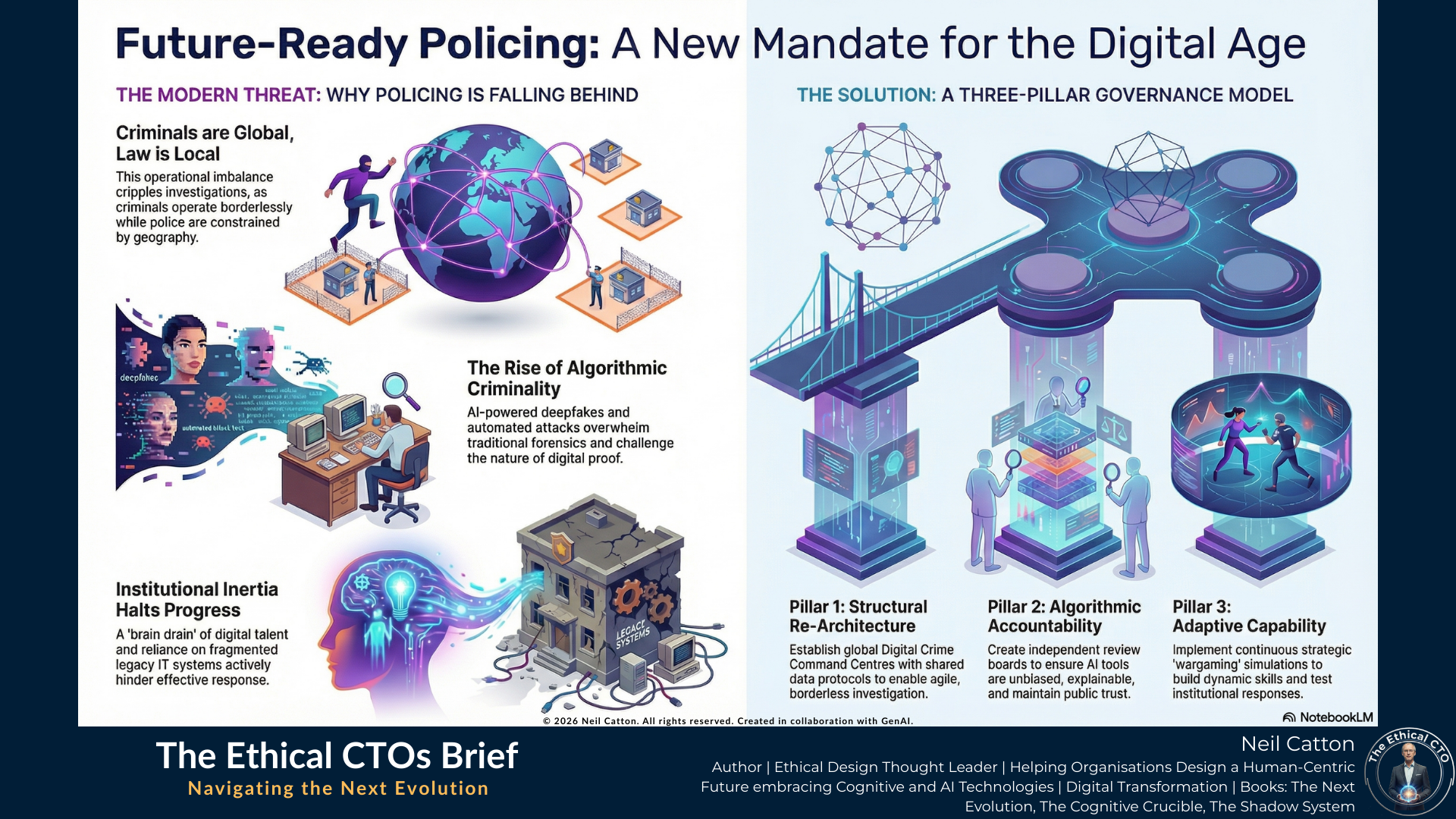
The Death of Geography: Why the "territorial" model of policing is failing in a non-localised threat landscape.
The Three-Pillar Framework: A structural look at integrating Digital Governance, Cognitive Augmentation, and Ethical Oversight.
Human-Centric Resilience: Why the ultimate goal of high-tech policing must be the restoration of low-tech human trust.
It’s time to move beyond "catching up" and start architecting a force that is as agile, interconnected, and resilient as the networks it seeks to protect.
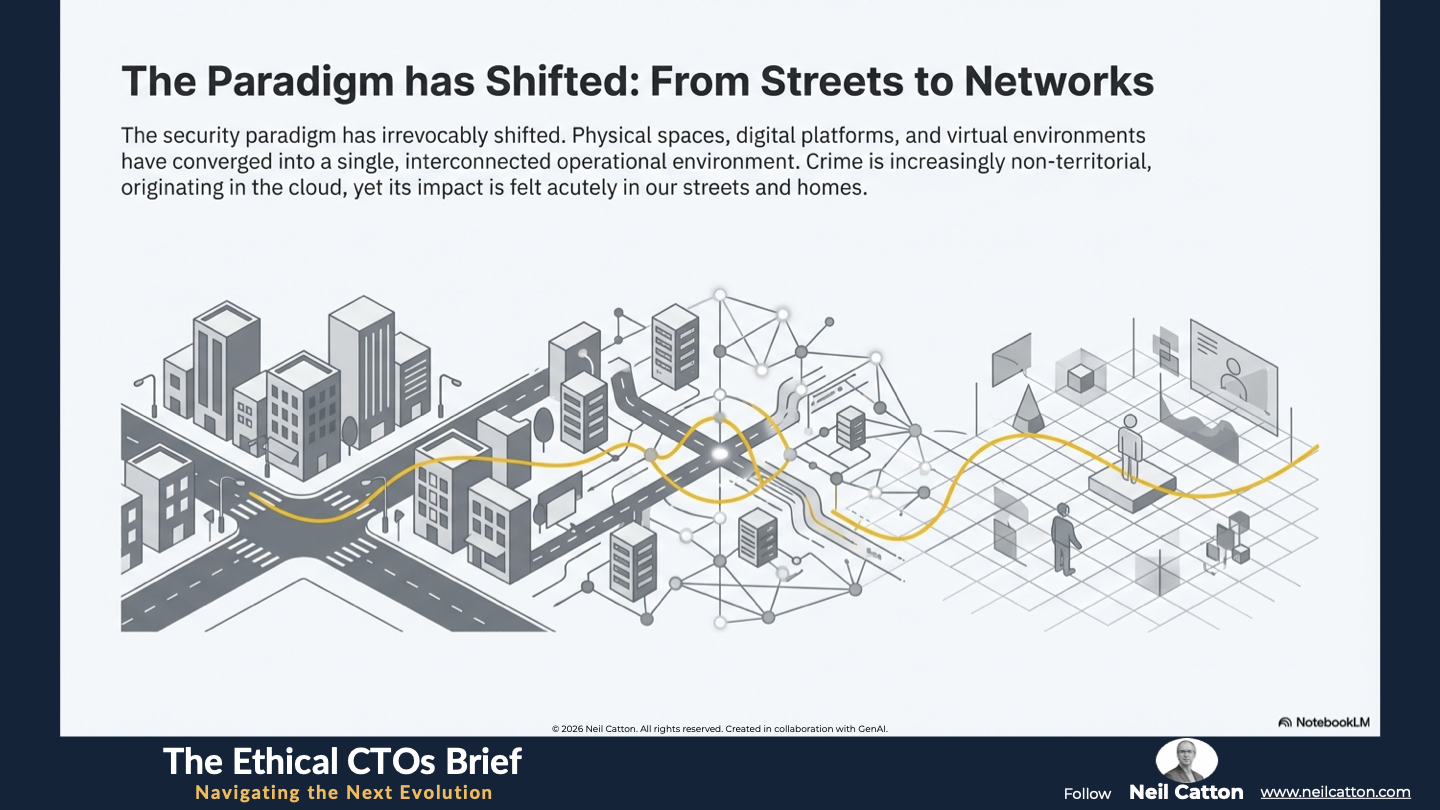
The Erosion of Boundaries: From Streets to Networks
The security paradigm has irrevocably shifted. We now live in a world where physical spaces, digital platforms and emerging virtual environments are seamlessly converging. This profound interconnectedness, while driving global commerce and fostering unprecedented social interaction, has simultaneously created an ideal operational environment for organised crime and hostile state actors. Law enforcement agencies, once defined by geographical borders, now face sophisticated non-localised threats. Crime is increasingly non-territorial, originating in the cloud and transacting across decentralised systems. Its impact is felt acutely in our streets and homes, from shutting down hospital networks to large-scale financial fraud.
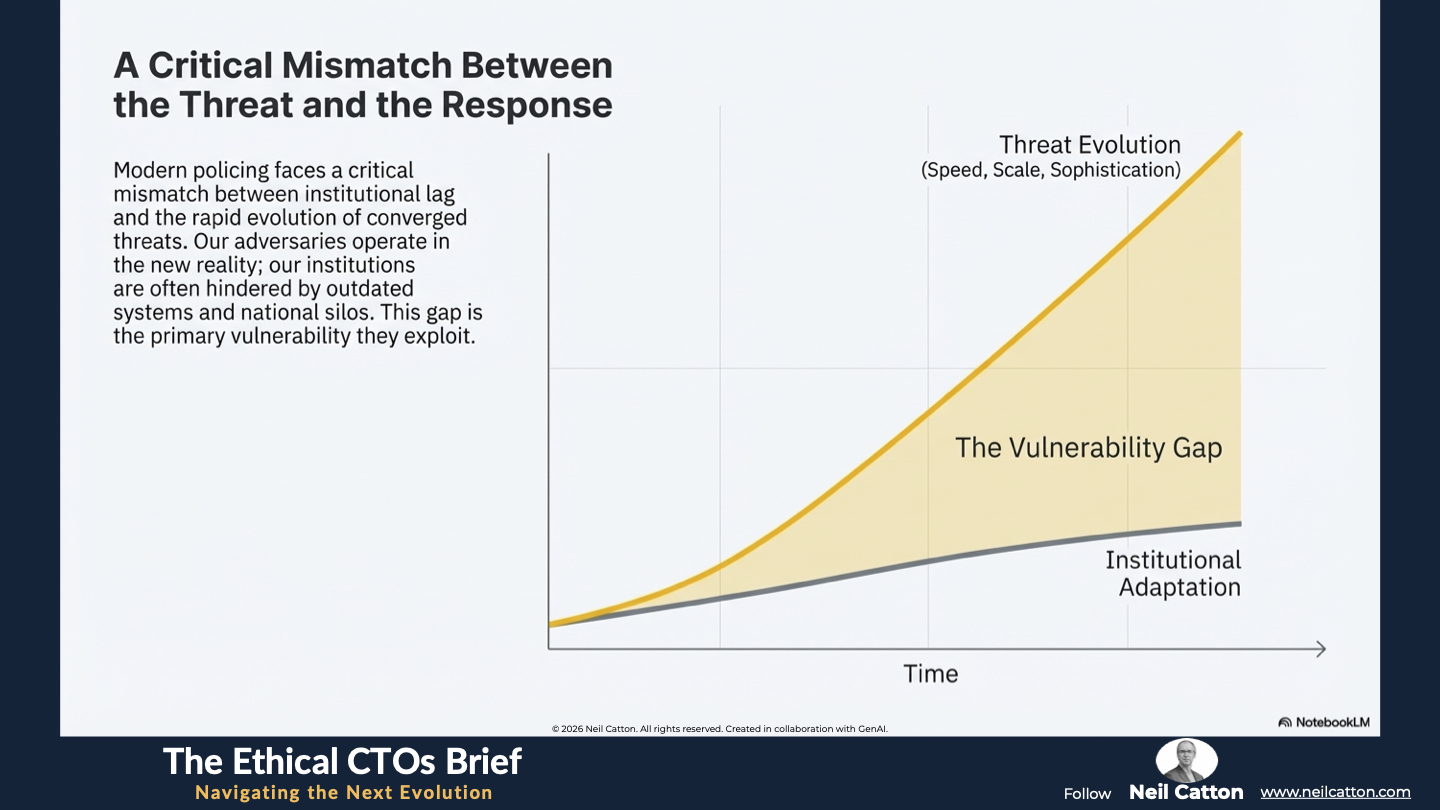
Modern policing faces a fundamental problem: a critical mismatch between institutional lag and the rapid evolution of cyber threats. Adversaries are gaining ground thanks to network effects, readily available AI tools and cryptographic anonymity. Meanwhile, the institutions responsible for public safety are often hindered by outdated systems, complex legal processes and national silos. This regulatory and technological gap is the main vulnerability cyber-adversaries exploit. To close this dangerous gap and regain control, policing must abandon incremental change and adopt a unified strategic governance framework that adapts to the constant convergence of technology and security.
 Understanding the Contemporary Challenge
Understanding the Contemporary Challenge
Having established the fundamental shift in the security landscape, we must now explore the mechanics of today’s sophisticated threat. Operational reality has transcended simple cybercrime into a world of algorithmic criminality. This current criminal ecosystem is professionalised, globally distributed and technologically advanced, characterised by three escalating dynamics demanding a radical shift in policing strategy.
The Operational Asymmetry of Globalised Crime
The internet’s ultimate decentralising power renders geographical borders practically meaningless for criminal logistics. This creates a massive operational imbalance: criminals are global while the law remains national. Consider the logistics of a typical sophisticated attack. A ransomware campaign could be orchestrated from a single server farm in one jurisdiction, utilising a complex web of anonymous command-and-control infrastructure. This would target thousands of critical victims across multiple continents. The resulting ransom payments would then be laundered instantly through decentralised finance (DeFi) platforms and intricate crypto mixers.
The consequences for law enforcement, whether it’s the Metropolitan Police in London or a national agency, are profound. The crime is instant, borderless and fast-moving but the investigative response remains slow, geographically constrained, and often critically delayed by the glacial pace of traditional legal instruments like Mutual Legal Assistance Treaties (MLATs). This asymmetry is a crippling vulnerability. The response must match the threat’s nature: effective counter-measures demand seamless international cooperation not just as a desirable outcome, but as a mandated baseline requirement for forensic analysis, operational response, and recovery. Until law enforcement structures reflect the global nature of criminal networks, policing will remain perpetually on the back foot.
The Rise of Algorithmic Criminality: Automation and Deception
Digital crime has evolved beyond small-scale opportunists. It’s becoming increasingly automated, intelligent, and designed for maximum scale. Organised syndicates now leverage advanced technology to amplify their operations’ scale and complexity, pushing the fight into the realm of artificial intelligence.
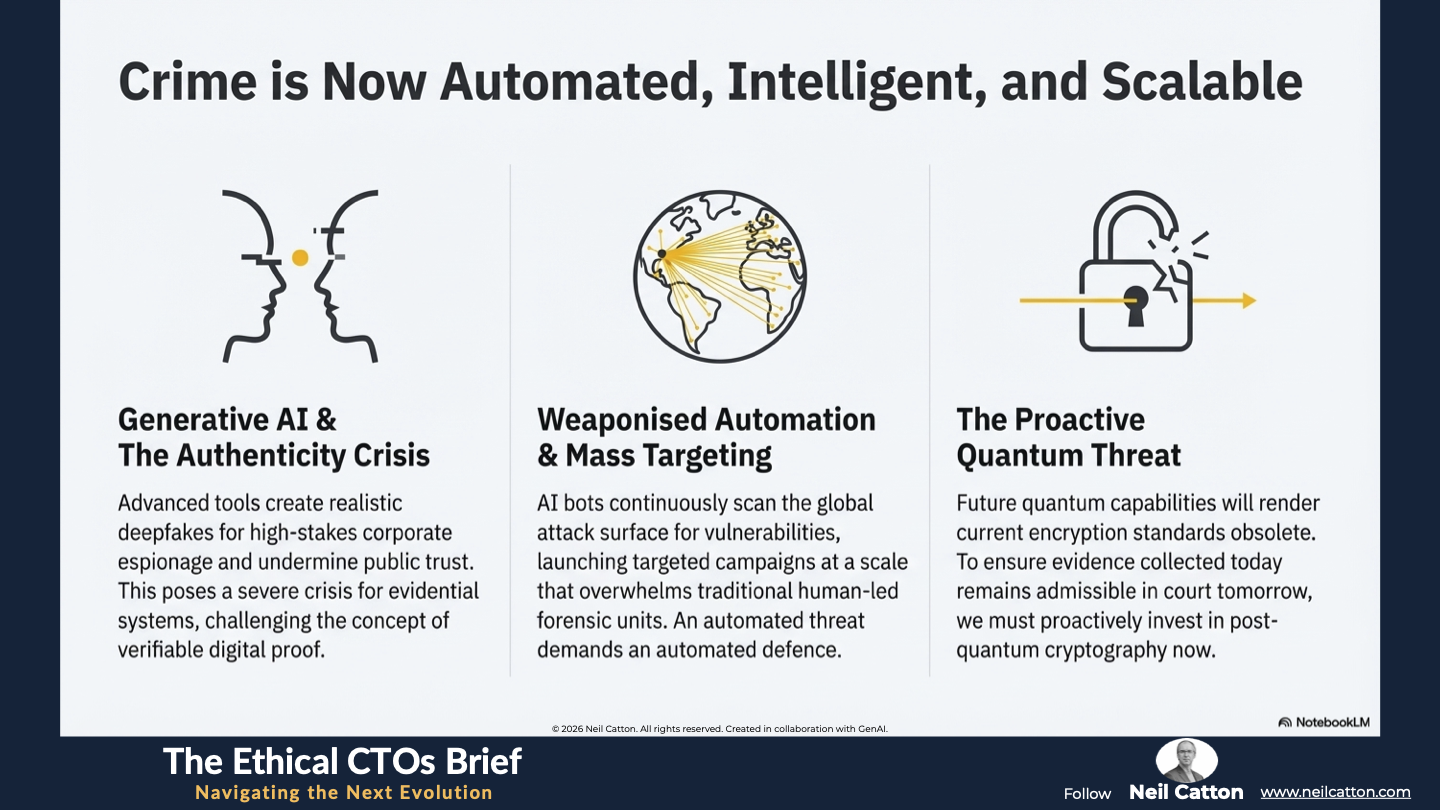
- Generative AI and the Authenticity Crisis: The rapid rise of advanced generative AI tools allows criminals to create incredibly realistic deepfake audio and visual content. This capability is exploited for high-stakes corporate espionage, such as impersonating a CEO or senior executive to authorise massive fraudulent payments. It also undermines public trust by fabricating crises. This technology poses a severe crisis of authenticity for evidential and legal systems, challenging the very concept of verifiable digital proof. AI-generated malicious code or zero-day vulnerability identification accelerates the attack lifecycle far beyond human defence capabilities.
- Weaponised Automation and Mass Targeting: Advanced AI bots continuously and automatically scan the entire global attack surface, searching for weaknesses in network perimeters. Once vulnerabilities are found these systems launch perfectly timed and highly targeted social engineering and intrusion campaigns. The sheer volume of digital evidence generated by such large-scale automated attacks overwhelms traditional police forensic units, making manual processing and triage impossible. This automated threat demands an automated defence.
- The Proactive Quantum Threat: Although full quantum computing is still developing, the need for moral foresight means the quantum threat is immediate. Future quantum capabilities will render current encryption standards – the cornerstone of secure communication and digital evidence – obsolete. Consequently, law enforcement must proactively invest today in post-quantum cryptography, quantum-safe storage, and data integrity protocols. This forward-thinking investment is crucial to ensure critical evidence collected now can still be accessed, verified, and admitted in court years from now long after the quantum era arrives. Failure to prepare risks losing decades of investigative history.
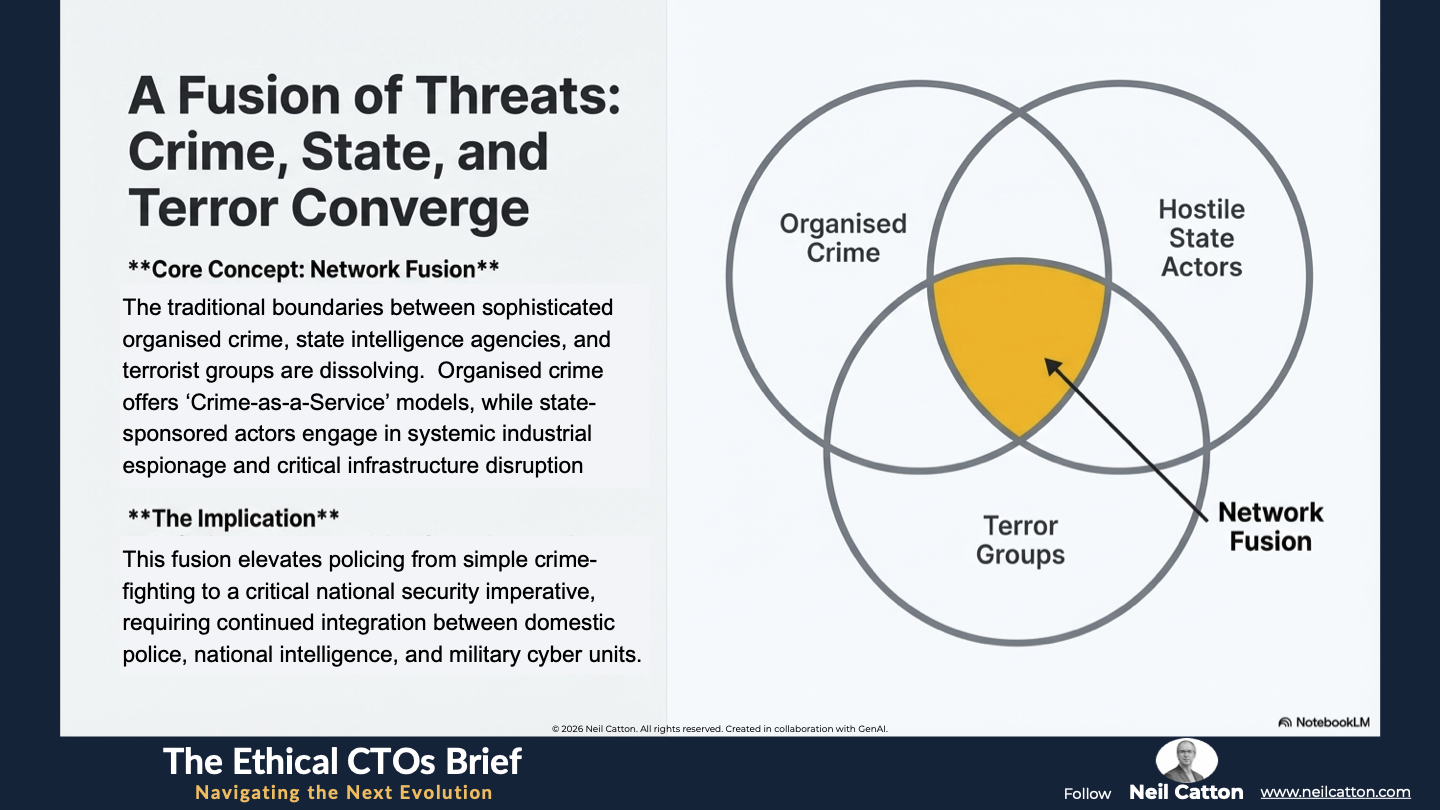
Network Fusion: The Convergence of Crime, State, and Terror
The traditional clear-cut boundaries between different threat actors have blurred. Today’s operational lines between sophisticated private-sector organised criminal networks, state intelligence agencies, and terrorist groups are increasingly ambiguous – a phenomenon I call Network Fusion. Organised crime groups operate with the commercial efficiency of global corporations offering ‘Crime-as-a-Service’ models like Ransomware-as-a-Service. This lowers the barrier to entry for low-skilled affiliates. Simultaneously state-sponsored actors employ cyber warfare for systemic industrial espionage, intellectual property theft ,and the intentional disruption of critical national infrastructure such as energy grids, financial systems, and healthcare services. This fusion elevates policing from simple crime-fighting to a critical national security imperative. It demands urgent operational integration of domestic police cyber command with national intelligence services and military cyber defence units. A threat this complex and multifaceted cannot be defeated by a single agency working in isolation.
The Inertia of Institutions
The modern threat landscape’s profound complexity and staggering speed reveal the fundamental operational legal and structural limitations of current law enforcement. To transition effectively from a reactive analogue force to a proactive digital one, policing must first address its internal failures and the systemic challenges causing regulatory delays. This isn’t a budget issue but a deep-seated governance and organisational design problem.
The Human Capital Crisis: Skills and Capability Drain
The most pressing crisis is the structural shortage of personnel with high-end digital expertise. Police forces simply can’t compete with the salaries, modern working environments, and career mobility offered by the private tech sector. This disparity goes beyond pay; the rigid hierarchical and often slow-moving bureaucratic culture of public service stifles the innovative mindset needed for top data scientists and cybersecurity professionals. This cultural clash fuels a constant ‘brain drain’ and results in a critical loss of talent.
- Loss of Institutional Knowledge: Reliance shifts to expensive, short-term external contractors, preventing the internal development of sustainable, proprietary expertise and the retention of long-term institutional memory necessary for complex, multi-year investigations.
- Erosion of Trust: The force becomes dependent on external, non-vetted personnel for core investigative functions, introducing significant vulnerabilities in terms of data integrity and security clearances. The capability to police the digital domain must be sovereign, residing within the force itself, not outsourced.
The Constraint of Legacy Systems and Data Silos
Many law enforcement agencies in the UK and internationally depend on ageing, fragmented and often custom-built IT infrastructures. These legacy systems aren’t just inefficient; they actively hinder effective investigation into crimes that cross digital and physical boundaries. For example, a cyber intrusion might precede a physical theft, spreading crucial evidence across multiple non-communicating databases like a national cyber registry, local force records, financial systems and forensic lab logs.
The consequence is a crippling operational failure:
- Incompatible Formats: Investigators are forced to manually correlate and reconcile data fields between systems that were never designed to speak to one another, wasting time and allowing the criminal advantage to increase.
- Departmental Silos: This failure is a direct result of decades of siloed, department-specific procurement cycles. As long as individual departments maintain 'data ownership' as a political power-base, the essential goal of data interoperability, the cornerstone of efficient public service, remains unattainable, fatally undermining collaborative investigation.
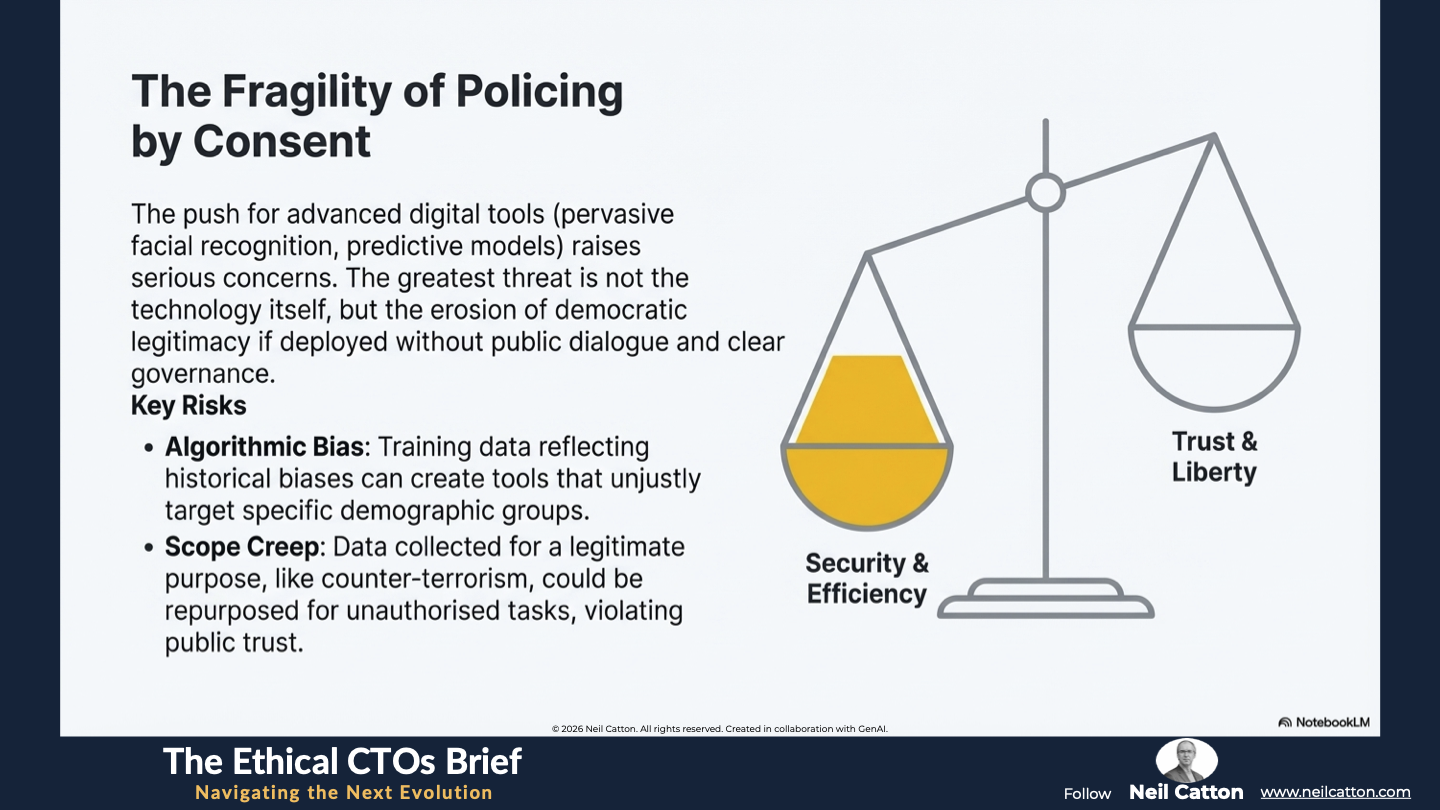
The Ethical Dilemma and the Fragility of Public Trust
The push for advanced digital policing tools like pervasive facial recognition and deep-learning predictive models, raises serious concerns about privacy, civil liberties, and algorithmic fairness. While these tools undoubtedly improve efficiency, their widespread adoption carries significant risks unless properly regulated.
The greatest threat isn’t the technology itself but the erosion of policing by consent. Advanced capabilities deployed secretly without public dialogue, judicial oversight, or clear governance undermine the force’s democratic legitimacy. Specific risks include:
- Algorithmic Bias: If the underlying datasets used to train AI models reflect historical biases, the resulting tool can unjustly target specific demographic or socio-economic groups, creating systemic injustice.
- Scope Creep and Data Integrity: There’s a constant risk that data collected for a legitimate purpose, like counter-terrorism, could be repurposed for entirely different, unauthorised tasks such as minor traffic violations. This violates the public’s implicit agreement about their data privacy.
The shift from a reactive analogue force to a proactive digital one isn’t simply a technology project; it’s a fundamental governance overhaul. This demands a structural and ethical transformation to maintain public trust.

The Three-Pillar Governance Model
To secure the converging world, law enforcement must adopt a strategic framework that future-proofs the entire institution. This is achieved through the Three-Pillar Governance Model, which simultaneously addresses systemic failures in jurisdiction, ethics, and adaptation. It demands a fundamental shift in institutional behaviour moving from a fragmented reactive approach to a globally coordinated, ethically rigorous, and continuously adaptive system.
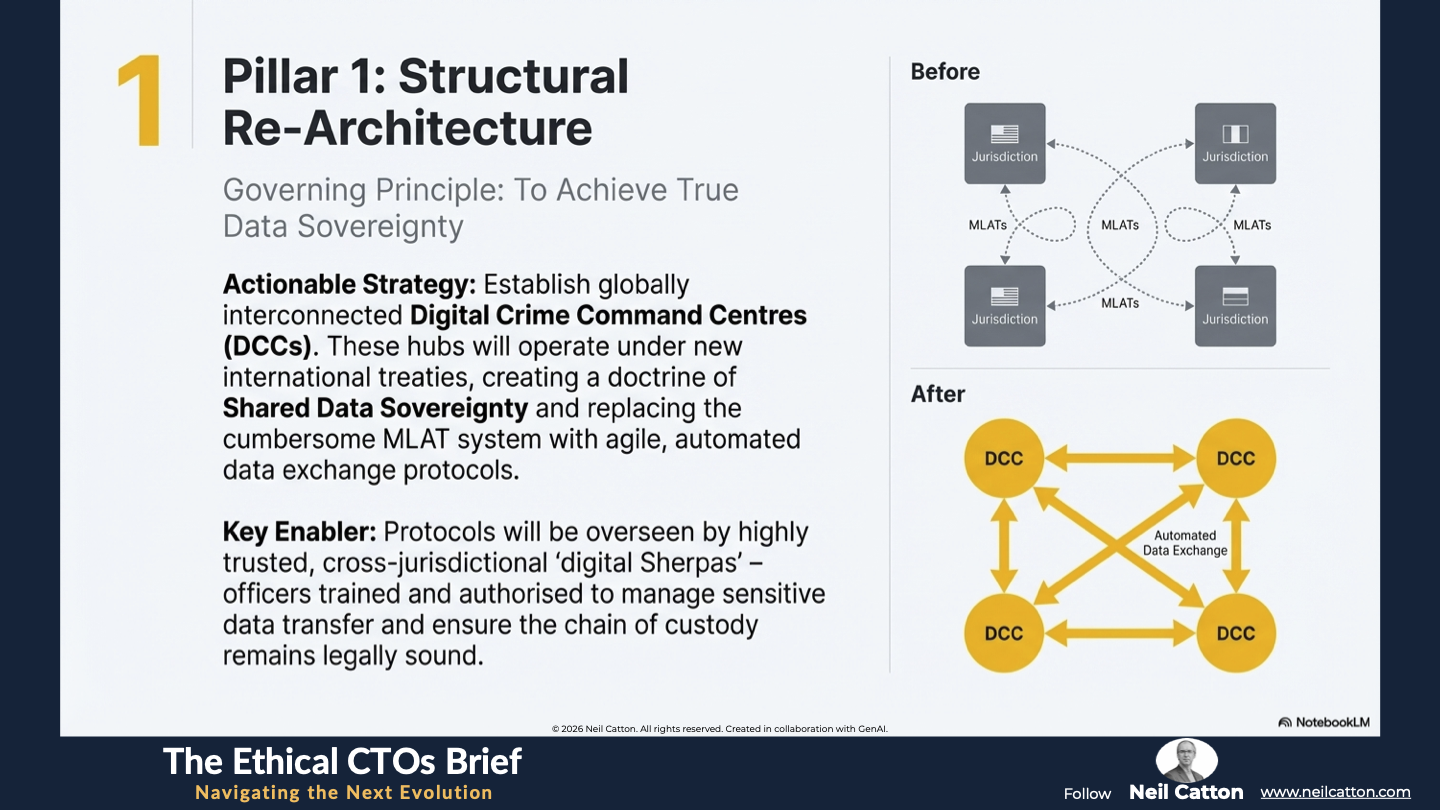
Pillar 1: Structural Re-Architecture for Data Sovereignty
The fundamental problem lies in the inability to manage data flow across borders. This renders the idea of national data sovereignty a impractical defence against non-territorial crime. A radical structural shift away from purely national responses is needed.
- Actionable Strategy: Digital Crime Command Centres (DCCs) and Shared Data Protocols: Rather than simply bolstering existing national forces, we need to establish globally interconnected specialised Digital Crime Command Centres. These hubs would function under new international treaties granting harmonised investigative powers and establishing a doctrine of Shared Data Sovereignty. This replaces the cumbersome MLAT system with agile automated data exchange protocols. Crucially these protocols must be overseen by highly trusted cross-jurisdictional ‘digital Sherpas’ – officers specifically trained and authorised to manage sensitive data transfer. This ensures the chain of custody remains legally sound and admissible in various legal systems. This structural shift places the investigation’s focus on the digital evidence itself, irrespective of national boundaries.
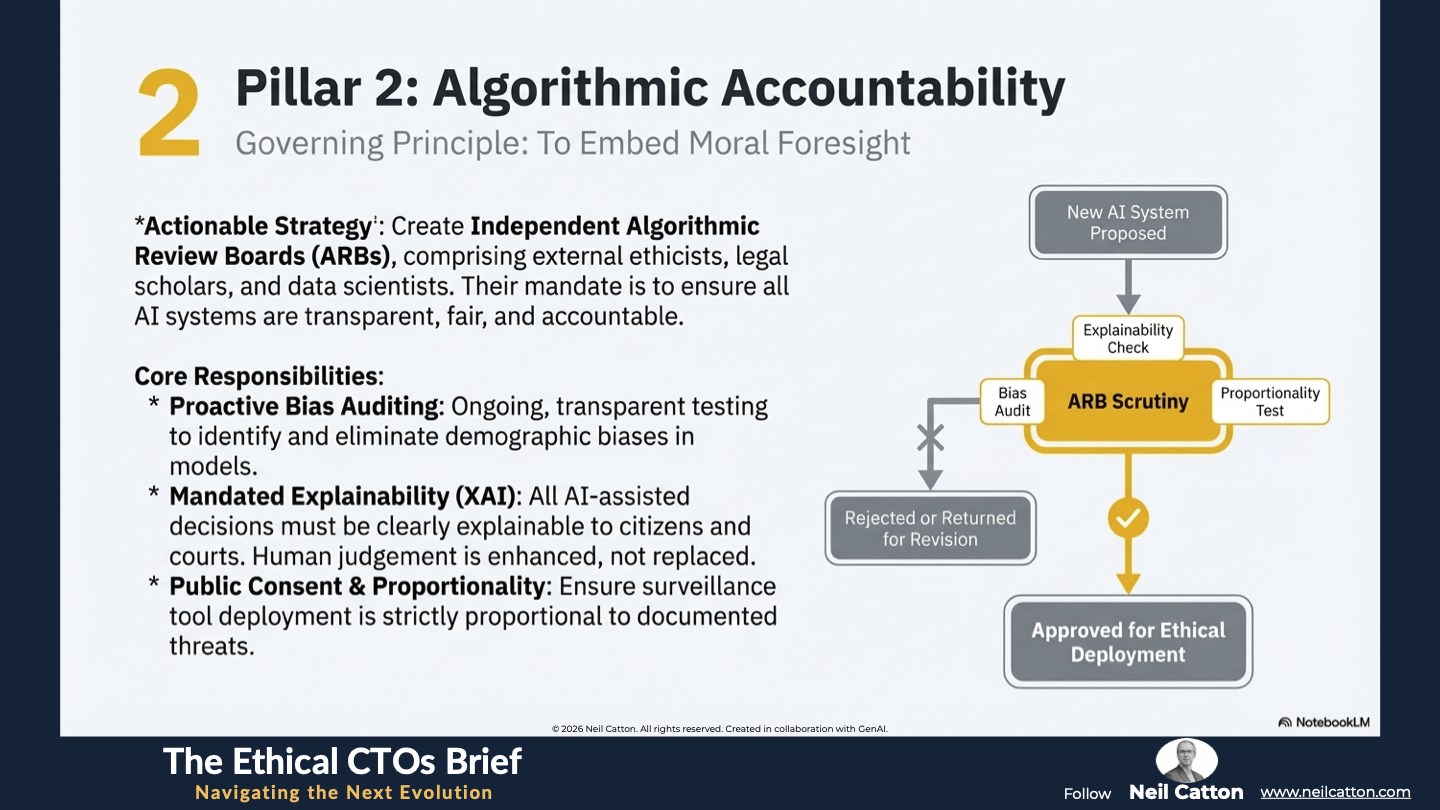
Pillar 2: Algorithmic Accountability and Moral Foresight
The unavoidable integration of AI into policing demands a multifaceted approach, encompassing both technical and moral considerations. This Pillar emphasises the importance of embedding Moral Foresight within institutions. It involves the ability to anticipate model and mitigate the ethical and social risks associated with new technology prior to its deployment.
- Actionable Strategy: Independent Algorithmic Review Boards (ARBs): To ensure accountability and maintain public trust, all policing AI systems must undergo rigorous independent scrutiny. This necessitates the creation of independent Algorithmic Review Boards (ARBs) comprising ethicists, legal scholars, and data scientists, all external to the police force. Their responsibilities encompass:
- Proactive Bias Auditing: Ongoing, transparent testing of AI models is essential to identify and eliminate demographic biases. This includes ensuring predictive models don’t unfairly target specific socio-economic groups.
- Mandated Explainability (XAI): All AI-assisted decisions must be transparent and clearly explainable to citizens and courts. The technology should function as a rigorous analytical tool but never replace the essential human accountability and judgement required in policing.
- Public Consent and Proportionality: Governance over mass surveillance tools must be rigorous. Deployment should be strictly proportional to documented threats and always prioritise the fundamental privacy rights of the public.
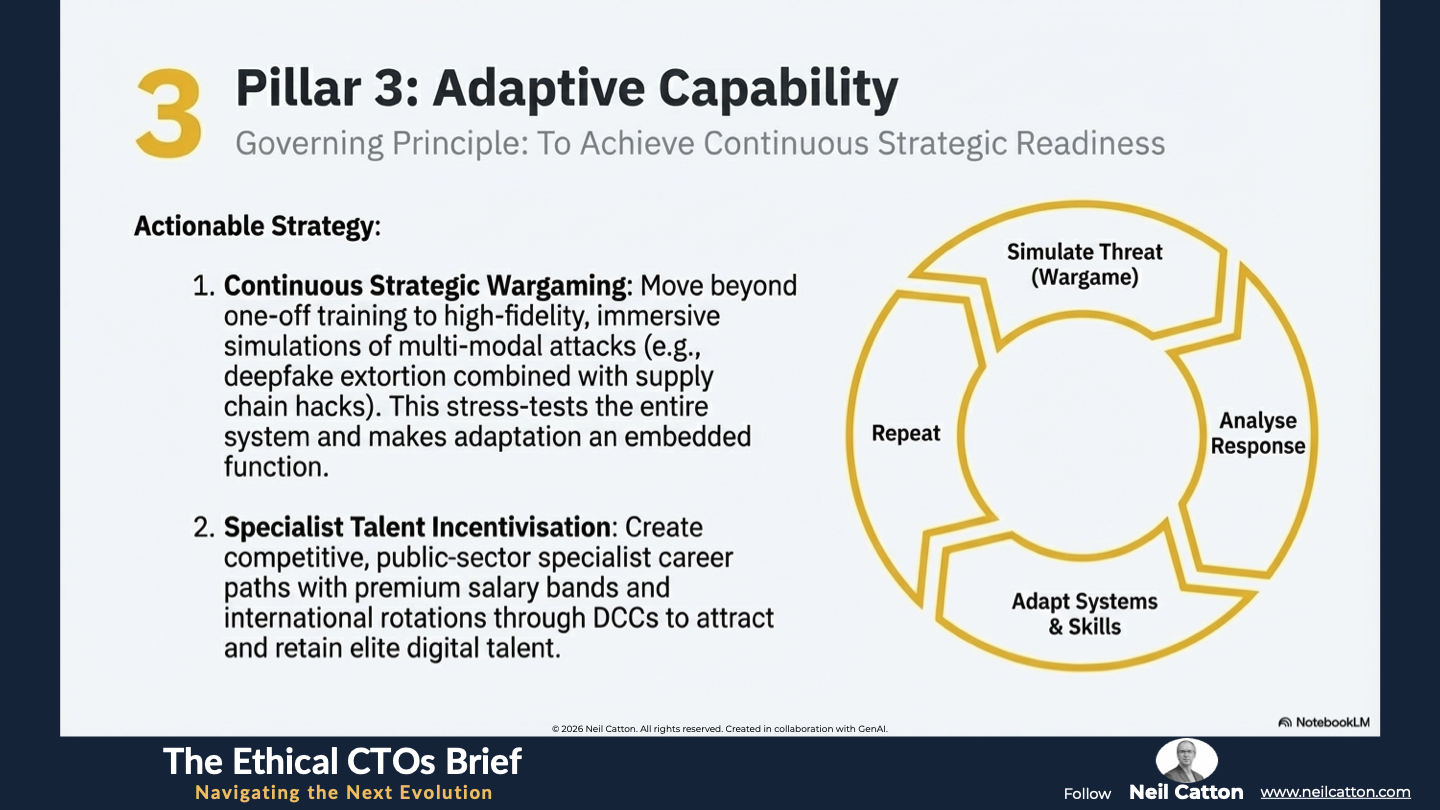
Pillar 3: Adaptive Capability through Continuous Strategic Wargaming
A future-ready police force’s operational capacity must be dynamic, built around a mechanism for continuous adaptation. This systemic approach will manage perpetual technological change and talent development effectively.
- Actionable Strategy: Traditional, one-off training is insufficient for modern security challenges. Therefore, the pillar on Embedded Strategic Wargaming Programmes advocates for a shift towards Continuous Strategic Wargaming Programmes. These high-fidelity, immersive simulations involve multi-modal attacks like coordinated deepfake extortion and logistical supply chain hacks. They stress-test the operational and ethical responses of the DCCs and ARBs. This approach transforms threat adaptation into a fundamental, embedded function of the police organisation.
- Specialist Talent Incentivisation and Retention: To address the human capital crisis, policing needs to develop competitive public-sector specialist career paths. This involves creating premium salary bands offering substantial benefits and rotating staff through international District Command Centres. By making public service a genuinely appealing option for top cybersecurity and data science graduates, we secure the high-level expertise needed to manage these complex systems and protect the institution’s integrity.
A Final Word
The world is converging and policing must adapt. The challenges posed by algorithmic crime, data sovereignty, and ethical surveillance aren’t isolated problems but rather symptoms of a fundamental disconnect between traditional governance and the digital world. A solution isn’t found in new technology alone but in a new structural mandate – the Three-Pillar Governance Framework.
By adopting Structural Re-Architecture, enforcing Algorithmic Accountability and building Adaptive Capability, we can close the regulatory gap currently empowering criminals. Failure to implement this systems approach risks a future where cybercrime remains unchecked, economies are continually undermined, and the rule of law is eroded by technological advances.
This strategic pivot demands leadership that values Moral Foresight and is prepared to overhaul institutions from the ground up. Integrity and effectiveness must become the cornerstones of the digital age. Policymakers face a stark choice: embrace the necessary systemic redesign outlined in this framework or accept a future characterised by perpetual operational asymmetry. The cost of incremental reactive change has shifted beyond mere efficiency losses; it now involves the rapid erosion of trust and the fundamental weakening of national security. This isn’t a theoretical modernisation exercise; it’s an urgent declaration of intent to govern the digital age. Securing a unified front against a non-territorial algorithmic threat demands strategic implementation. The time for debate is over; the time for action is now.
Key Takeaways: Architecting the Agile Force
Pillar 1: Structural Re-Architecture: Implementing Digital Crime Command Centres and "Shared Data Sovereignty" to match the borderless nature of cyber-adversaries.
Pillar 2: Algorithmic Accountability: Establishing Independent Algorithmic Review Boards (ARBs) to audit bias and ensure "Mandated Explainability" (XAI).
Pillar 3: Adaptive Capability: Embedding Continuous Strategic Wargaming to stress-test ethical and operational responses against multi-modal attacks.
Human-Centric Resilience: Shifting the goal from "catching criminals" to restoring public trust through transparency and moral foresight.
Strategic Insights: Clouds, Codes, and Crime: The Security Paradigm
Operational Asymmetry: Why criminals are global while law remains national—and how Shared Data Protocols solve the MLAT delay.
Network Fusion: The convergence of Crime-as-a-Service, state-sponsored industrial espionage, and critical infrastructure disruption.
The Quantum Threat: Why we must invest in post-quantum cryptography today to protect digital evidence integrity for the future.
The Authenticity Crisis: How Generative AI and deepfakes are weaponised for high-stakes corporate espionage and fraudulent payments.
Video Summary: From Pavements to Networks: Securing the Future
The Death of Geography: Why traditional borders no longer define the threat landscape.
The Human Capital Crisis: Overcoming the "brain drain" to the private sector by creating premium public-sector career paths for digital talent.
Legacy System Drag: How departmental data hoarding fatally undermines collaborative investigation and interoperability.
The Proactive Mandate: Why leadership must value "Moral Foresight" to govern a world where all modern conflict lives in the cloud.
The Ethical CTO: Arc 2 Index
- The Speed of Change: Governing the Tempo
- Where Policy Fails: The Governance Gap
- The Strategic Bridge: Closing the Gap
- Breaking the Structural Barriers : Data Silos
- The new OS of Society: Governing the Algorithmic State
- The human cost of exclusion: The Algorithmic Abyss
- Designing for Civic Agency: The Ethical Architect
- Trust in the age of AI: Policing at an Inflection Point
- The zenith of converged security: Designing the Future-Ready force